LIMS Qualification for Analytical Data Management
1. Purpose and Scope
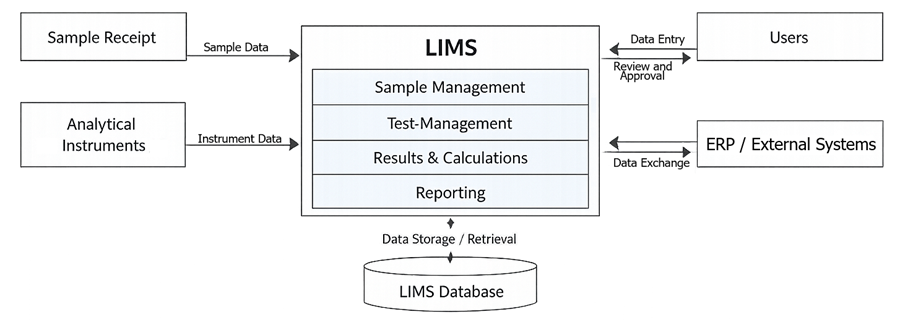
A Laboratory Information Management System (LIMS) is a critical computerized system used to manage analytical data, sample lifecycle, test execution, and reporting in regulated laboratory environments. Qualification ensures the system is fit for intended use, maintains data integrity, and complies with regulatory requirements.
2. Role of LIMS in Analytical Data Management
LIMS serves as the central control point for analytical workflows. Core functions include:
- Sample registration and lifecycle tracking
- Test assignment and scheduling
- Data capture and result entry
- Calculations and specification evaluation
- Report generation and approval
- Data storage, retrieval, and archival
LIMS typically integrates with analytical instruments, CDS, and enterprise systems. It is a high-impact GxP system. The diagram below illustrates the position of LIMS within the analytical data environment. It shows how samples, analytical instruments, and external systems interact with LIMS, and how data is collected, processed, and stored within a centralized system.
3. Risk-Based Qualification Approach
Qualification depth is driven by system complexity and risk.
3.1 Typical Risk Factors
Risk assessment determines the depth and scope of LIMS qualification. Each factor reflects how the system can influence data reliability, regulatory compliance, and product quality.
- Impact on product quality decisions: Evaluate whether LIMS data is used for critical decisions such as product release, stability acceptance, or investigation outcomes. Systems directly supporting release or regulatory reporting carry the highest risk and require comprehensive qualification and strict controls.
- Degree of system configuration or customization: Assess how extensively the system is configured or customized to support laboratory processes. Standard configurations present lower risk, while complex configurations and custom logic increase the likelihood of errors affecting data processing or workflow execution. Higher complexity requires deeper functional verification.
- Complexity of workflows and calculations: Consider the number of workflow steps, conditional logic, and calculation rules implemented in the system. Complex workflows and derived calculations increase the risk of incorrect data processing or unintended outcomes. Qualification must verify all logic paths, including boundary and exception conditions.
- Number and type of integrations: Evaluate connections with instruments, CDS, ERP systems, or external databases. Each integration introduces potential failure points such as data loss, duplication, or mapping errors. Systems with multiple or complex integrations require thorough interface testing and data reconciliation controls.
- Use of electronic records and signatures: Determine whether the system manages regulated electronic records and applies electronic signatures. This introduces requirements for compliance with 21 CFR Part 11, including audit trails, user authentication, record protection, and signature traceability. Systems using these features require focused verification of compliance controls and data integrity safeguards.
3.2 System Classification Elements
System classification defines the level of validation rigor required. It is not a label but a structured evaluation of how the LIMS is implemented, configured, and used within the regulated environment.
- Configured commercial off-the-shelf system: The LIMS is supplied as a standard vendor product with predefined functionality. Implementation is based primarily on configuration rather than custom code development. Risk is introduced through configuration choices such as workflow setup, calculation parameters, and user roles. Qualification must verify that configured elements correctly implement intended laboratory processes and do not introduce unintended behavior.
- Customized workflows and logic: The system includes user-defined workflows, calculations, or business rules beyond standard configuration. This may involve complex test logic, derived calculations, specification handling, or conditional process flows. These elements increase risk because errors can directly affect analytical results or decisions. Qualification must include detailed functional testing of all custom logic, including boundary conditions and failure scenarios.
- Integrated system environment: The LIMS exchanges data with other systems such as analytical instruments, chromatography data systems, ERP, or external databases. Integration introduces dependency on data transfer mechanisms, mapping accuracy, and synchronization between systems. Failures may lead to data loss, duplication, or misinterpretation. Qualification must verify interface reliability, data integrity across transfers, and controlled handling of integration errors.
- Regulatory data management system: The LIMS manages GxP data used for product release, stability studies, investigations, or regulatory submissions. As a result, it is subject to strict data integrity and compliance requirements. This classification drives the need for controls such as audit trails, electronic signatures, access management, and validated data lifecycle processes. Qualification must demonstrate that the system enforces these controls consistently and that records are trustworthy, complete, and traceable.
4. User Requirements Specification (URS)
URS defines intended use and all required system capabilities. URS must include:
- Sample lifecycle management requirements
- Test and specification management
- Result entry and calculation logic
- Workflow and approval processes
- Reporting requirements
- User roles and access control
- Audit trail requirements
- Data storage, backup, and archival
- Integration requirements
- 21 CFR Part 11 compliance expectations
All requirements must be testable and traceable.
5. System Design and Configuration
LIMS is configured based on URS. Configuration elements:
- Sample workflows and status logic
- Test methods and specifications
- Calculation formulas and limits
- User roles and permissions
- Approval workflows
- Interface definitions
Configuration must be documented and traceable to URS.
6. Installation Qualification (IQ)
The diagram below presents the lifecycle approach used for LIMS qualification. It shows how user requirements and system configuration lead into Installation Qualification, Operational Qualification, and Performance Qualification, followed by ongoing lifecycle control through change management and periodic review.

6.1 Objective
Verify that the LIMS environment is installed correctly and matches approved specifications, including infrastructure supporting data protection such as backup and storage configuration.
6.2 IQ Protocol Content
IQ protocol must include:
- Purpose and scope
- System description including architecture
- Hardware and software inventory
- List of required components and versions
- Installation verification steps
- Network and security configuration requirements
- Database configuration verification
- Backup infrastructure and storage configuration requirements
- Environmental requirements if applicable
- Reference to vendor documentation
- Acceptance criteria
- Deviation handling instructions
6.3 IQ Test Execution
Execution is verification-based, not functional testing.
Activities:
- Server installation and configuration confirmed against specification
- Operating system and patch level documented and aligned with requirements
- LIMS software installation and version confirmed
- Database installation and configuration confirmed
- Application services status confirmed as operational
- Network connectivity and user access confirmed
- Security configuration baseline confirmed
- Supporting software components confirmed as installed
- Backup infrastructure installed and configured as specified
- Backup storage locations defined and accessible
- Required backup-related services or agents active
Execution principles:
- Use objective evidence such as screenshots, system outputs, and configuration files
- Record actual values and compare to expected
- Document any deviations
6.4 IQ Acceptance Criteria
- All components installed per specification
- System environment matches defined baseline
- Backup infrastructure and storage configuration are correctly implemented
- No critical deviations impacting system readiness
7. Operational Qualification (OQ)
7.1 Objective
Verify that the LIMS functions operate correctly under controlled conditions.
7.2 OQ Protocol Content
OQ protocol must include:
- Purpose and scope
- Traceability to URS requirements
- Defined test scenarios covering all critical functions
- Test data requirements
- Step-by-step test scripts
- Expected results for each step
- Negative testing scenarios
- Data integrity verification steps
- Security and access control testing
- Audit trail verification
- Electronic signature testing
- Backup and archival function verification
- Acceptance criteria
- Deviation management
7.3 OQ Test Coverage
7.3.1 Functional testing:
- Sample registration and ID generation
- Sample lifecycle tracking and status transitions
- Test assignment and scheduling
- Result entry including manual and automated entry
- Calculation logic and specification enforcement
- Report generation and approval workflows
7.3.2 Data integrity controls:
- Audit trail creation and content verification
- Protection of original data
- Traceability of data changes
- Time-stamping and user attribution
7.3.3 Security testing:
- User authentication
- Role-based access control
- Access restriction enforcement
- Password and session controls
7.3.4 Electronic records and signatures:
- Signature application and linking to records
- Signature meaning and traceability
- Prevention of unauthorized approval
7.3.5 Integration testing (if applicable):
- Data transfer accuracy
- Handling of failed transfers
- Duplicate record prevention
- Data mapping verification
7.3.6 Backup and archival verification:
- Verification that backup jobs are configured and enabled
- Execution of backup process and confirmation of successful completion
- Verification of backup logs or status notifications
- Confirmation that backup failures are detected and recorded
- Execution of archival process according to defined rules
- Verification that archived records are protected from modification
- Retrieval of archived data through the application
7.3.7 Negative testing:
- Invalid data entry
- Unauthorized actions
- Workflow bypass attempts
7.4 OQ Test Execution
- Execute scripts exactly as written
- Use controlled test data
- Capture evidence for each step
- Record actual vs expected results
- Document all deviations immediately
Execution must demonstrate both correct operation and failure control, including verification that backup and archival processes execute and are properly controlled.
7.5 OQ Acceptance Criteria
- All critical functions operate as intended
- Data integrity controls function correctly
- Security controls are enforced
- Backup and archival functions operate correctly and are properly controlled
- All critical requirements are verified
- No unresolved critical deviations
7.4 OQ Test Execution
- Execute scripts exactly as written
- Use controlled test data
- Capture evidence for each step
- Record actual vs expected results
- Document all deviations immediately
Execution must demonstrate both correct operation and failure control.
7.5 OQ Acceptance Criteria
- All critical functions operate as intended
- Data integrity controls function correctly
- Security controls are enforced
- All critical requirements are verified
- No unresolved critical deviations
8. Performance Qualification (PQ)
8.1 Objective
Demonstrate that LIMS performs effectively under routine operating conditions, including the ability to retain, archive, and recover data as part of normal laboratory operations.
8.2 PQ Protocol Content
PQ protocol must include:
- Purpose and scope
- Defined representative workflows
- Identification of user roles
- Realistic data scenarios
- End-to-end process execution steps
- Acceptance criteria based on business process outcomes
- Data integrity verification within workflows
- Backup, archival, and data retrieval scenarios
- Documentation of user interaction
8.3 PQ Test Coverage
8.3.1 End-to-end workflows:
- Sample receipt through final disposition
- Routine analytical testing workflows
- Review and approval processes
- Report generation and release
8.3.2 Operational conditions:
- Use of typical users
- Use of production-like data
- Execution under normal workload conditions
8.3.3 Data lifecycle verification:
- Data creation
- Data modification and review
- Data approval
- Data storage and retrieval
8.3.4 Backup, archival, and recovery:
- Restoration of data from backup using recent dataset
- Confirmation that restored data is complete and usable
- Retrieval of archived data in a routine business context
- Verification that archived records remain readable and intact
8.4 PQ Test Execution
- Execute using trained users
- Follow actual SOP-based workflows
- Capture system behavior under real conditions
- Verify usability and process alignment
- Confirm no workarounds are required
- Execute data restoration and archival retrieval as part of workflow verification
8.5 PQ Acceptance Criteria
- System supports routine laboratory operations
- Workflows execute without failure
- Data integrity is maintained throughout lifecycle
- Backup restoration produces complete and usable data
- Archived data is retrievable and readable
- Users can perform tasks as intended
9. Data Integrity and Compliance Controls
The diagram below illustrates how LIMS enforces data integrity through multiple layers of system controls. It shows how access control, audit trails, electronic signatures, and data protection mechanisms collectively ensure that data meets ALCOA+ principles.
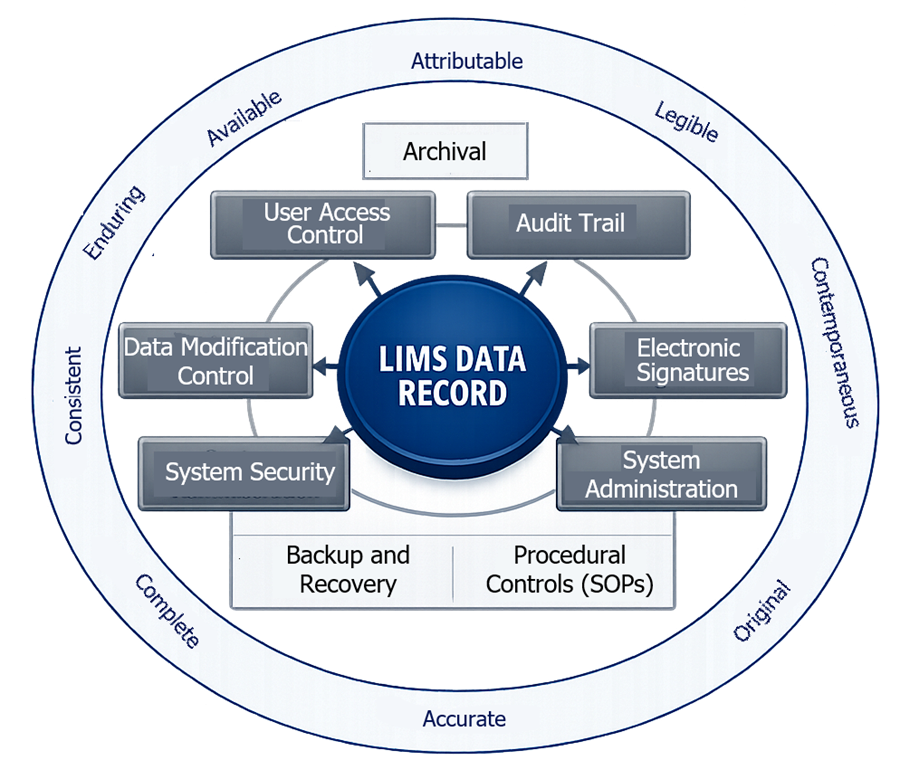
9.1 Required Data Integrity Controls
LIMS must implement technical and procedural controls that ensure analytical data is protected from unauthorized access, unintended modification, and loss. These controls are fundamental to maintaining data reliability and regulatory compliance.
- Unique user identification: Each user must have an individual account. Shared or generic accounts are not acceptable. User identity must be linked to all actions performed in the system, enabling traceability of data entry, modification, review, and approval.
- Role-based access control: System access must be restricted based on defined user roles and responsibilities. Permissions should be limited to the minimum required for each role. This prevents unauthorized data entry, modification, or approval and enforces segregation of duties.
- Secure audit trails: The system must automatically record all relevant actions, including data creation, modification, and deletion attempts. Audit trail entries must capture user identity, timestamp, original value, and new value where applicable. Audit trails must be secure, tamper-evident, and not editable by users.
- Controlled data modification: Any change to existing data must be controlled and traceable. The system must retain original entries and record the reason for change. Overwriting or deletion of original data without traceability is not acceptable.
- Electronic signature enforcement: Electronic signatures must be uniquely linked to individuals and require authentication at the time of use. Signatures must be permanently associated with the corresponding record and include the meaning of the signature such as review or approval.
- Data backup and recovery: Data must be protected against loss through routine backups and verified recovery procedures. Backup processes must ensure that complete and accurate data can be restored within defined timeframes following system failure or disruption.
9.2 Alignment with ALCOA+ Principles
These controls collectively ensure that data generated and managed in LIMS meets ALCOA+ expectations.
- Attributable: Every data entry and action is linked to a specific individual through unique user identification and audit trails.
- Legible: Data must be readable and understandable throughout its lifecycle, including after storage or archival.
- Contemporaneous: Data is recorded at the time the activity is performed, with accurate timestamps captured automatically by the system.
- Original: The system preserves original data entries or true copies, ensuring that the initial record is not lost or overwritten.
- Accurate: Data must reflect the actual observation or result. System controls such as validation rules and calculation verification support accuracy.
- Complete: All data, including metadata and audit trails, must be retained. No relevant information should be omitted.
- Consistent: Data must follow a logical and chronological sequence. Timestamps and workflow controls ensure proper order of events.
- Enduring: Data must remain intact and protected over time, including during storage, backup, and archival processes.
- Available: Data must be retrievable in a timely manner for review, audit, or inspection throughout the retention period.
10. Integration with Analytical Systems
Integration risks:
- Data transfer failures
- Partial or duplicate records
- Mapping errors
- Loss of traceability
Qualification requirements:
- Verify data transfer accuracy
- Test error handling and recovery
- Validate data reconciliation processes
- Confirm mapping between systems
11. Traceability and Documentation
Required documentation:
- User Requirements Specification
- Risk assessment
- Configuration documentation
- IQ, OQ, PQ protocols and reports
- Traceability matrix
- SOPs and work instructions
- Training records
12. Change Control and Lifecycle Management
Changes requiring assessment:
- Software updates or patches
- Configuration changes
- Workflow modifications
- Integration changes
- Security updates
Control activities:
- Impact assessment
- Regression testing
- Requalification as required
- Documentation updates
Periodic review must confirm continued compliance.
13. Backup, Archival, and Business Continuity
LIMS must ensure that analytical data remains protected, recoverable, and accessible throughout its entire lifecycle. Backup and archival controls are critical to prevent data loss, support regulatory inspections, and ensure continuity of laboratory operations in case of system failure or disaster events. Requirements:
- Defined backup procedures and frequency: Backup processes must be formally documented, including scope, method, and frequency. Backups should be performed at intervals appropriate to data criticality and system usage, ensuring that recent data can be recovered with minimal loss. Responsibilities for backup execution and monitoring must be clearly assigned.
- Secure storage of backups: Backup data must be protected against unauthorized access, alteration, or loss. Storage controls should include restricted access, encryption where appropriate, and physical or logical separation from the primary system. Offsite or cloud-based storage is typically required to mitigate site-specific risks.
- Periodic restoration testing: Backup effectiveness must be verified through documented restoration testing. These tests confirm that data can be successfully restored within defined timeframes and that restored data is complete, accurate, and usable. Restoration testing should simulate realistic recovery scenarios.
- Disaster recovery capability: A defined disaster recovery plan must ensure that the LIMS can be restored following major system failures such as hardware failure, cyber incidents, or facility disruptions. Recovery time objectives and recovery point objectives must be established and verified. Roles, responsibilities, and recovery procedures must be clearly documented.
- Long-term data archival: Analytical data must be retained for required regulatory periods in a format that remains readable and accessible. Archival processes must preserve data integrity, prevent unauthorized modification, and ensure that historical data can be retrieved for audits, investigations, or trending. Migration strategies may be required to maintain accessibility as technology evolves.
14. Summary
LIMS qualification must verify system installation, functionality, and performance in a structured, risk-based manner. IQ confirms correct installation. OQ verifies functional operation and data integrity controls. PQ confirms performance under real laboratory conditions. Proper execution ensures reliable analytical data and sustained compliance.

